You’ve heard it so many times that it probably sounds like a cliché at this point: the way we work has changed. But how, exactly, has it changed?

Your employees need the same level of network performance and security they would get if they worked in a central office, but they don’t work in the office. They work from kitchen tables, in airport lounges, and on public transit. Your IT team is tasked with protecting those users and delivering the reliability and productivity they’ve come to expect from a traditional network, but with a wildly different network topology and expanded perimeter. And – they must do it with limited time and strained resources, while still leveraging your existing investments.
Sounds easy, right? Spoiler alert – it’s not.
Even before the unprecedented shift to remote working in the first half of 2020, several key trends emerged over the past decade that have reshaped working styles. These changes led to changes in the networking and security landscape needed to support workers.
In this post, we’ve identified 10 key trends and challenges that have changed the game for networking and cybersecurity professionals.
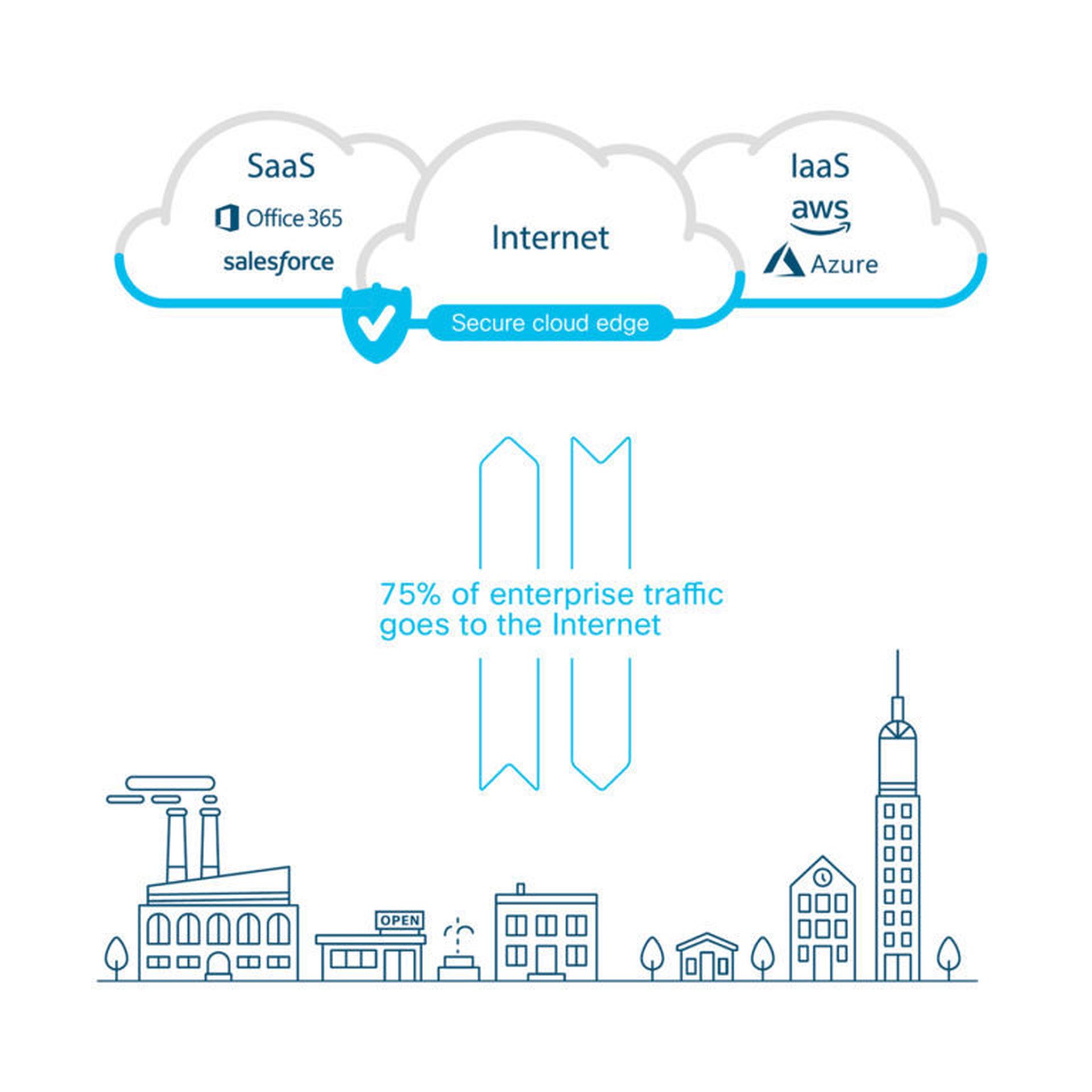
1. Increased cloud adoption
Over the past decade, public cloud usage has exploded in popularity. Every year, enterprises produce more data, and increasingly this data is being stored in software as a service (SaaS) applications in the public cloud. In 2019, Enterprise Strategy Group projected that 60 percent of organizations will use SaaS applications for greater than half of their business needs by 2021, and that number is only expected to increase.1 It’s essential to have strong security in place to protect that data no matter where it resides.
2. More network traffic
There’s been an explosion in the sheer amount of business data transferred over the corporate network – for example, just look at how much video content is created and shared today. Data-intensive applications require large amounts of network traffic, which creates demand for more bandwidth that strains existing network infrastructure and centralized security processes.
3. More remote and roaming workers
The new normal includes thousands of employees working from home, either temporarily or indefinitely. These users need to be protected as well as their counterparts at main office locations, even if their network traffic is going directly to the Internet. Most companies have VPN policies in place for employees working from home, but 85% of companies believe their employees regularly violate those policies.
A roaming worker is any employee that works from a home office or from another non-office location (like a client site or hotel room) at least one day a week. Though some workers are full-time roaming users (like traveling consultants), many other employees take on a “roaming user” role whenever they travel for business or work in a public place like a café. Roaming users need secure access to corporate resources even though they are outside the traditional network boundary.
4. More branch offices
When employees do work in an office, chances are good that they don’t all work in a single headquarters location. The days of all employees working together in one place are long gone for all except the smallest companies. As organizations expand into new markets, often by acquiring smaller companies and their office footprints, their number of branch offices grows too.
5. More network inefficiency
Traditionally, an organization would backhaul network traffic from branch offices and remote workers to headquarters to apply security policies, often using MPLS links. But as more data and devices join the network, that model leads to efficiency problems. Traffic destined for the Internet gets funneled to a headend (such as a corporate headquarters or data center) that directs it through a set of security checks and then provides Internet access — which creates a bottleneck.
6. Higher networking costs
Along with the increase in data and traffic, there’s been an increase in the cost of providing reliable network bandwidth to users. A traditional WAN connects users at branch or satellite locations and applications hosted on servers in a centralized data center. These connections are usually created with dedicated MPLS circuits. However, these dedicated circuits are costly to provision and maintain, and they don’t scale or adjust quickly as business needs change.
To combat this problem, 79% of organizations are either investigating, or already using, broadband direct internet access (DIA) at branch locations instead of backhauling traffic over MPLS. But DIA introduces new security challenges.
7. Performance issues with SaaS apps
Many businesses today use SaaS apps to conduct critical business functions, like sales operations, human resources, and general administrative work. But if those SaaS apps are set up to backhaul traffic using existing network links or VPN tunnels, users can experience latency, lost productivity, and frustration. When users experience performance issues with corporate-approved apps, they often turn to unauthorized and potentially risky apps to get their jobs done. More than 1,200 cloud services are used in the average large enterprise today, and as many as 98% of them are not approved by IT.
8. Security talent shortage
3.5 million cybersecurity jobs worldwide will not be filled by 2021. With unemployment on the rise, what’s the reason for this shortage? Qualified security professionals are difficult to find, expensive to hire, and tough to retain. Even when you do find a security rock star, your teams require significant investments in costly training to stay ahead of the latest security threats and networking challenges. The skills shortage leads to security blind spots, which can have a huge impact on organizations.
9. Too many security tools
Knowledge is power, but sometimes too much information is just that – too much! Remember those security professionals you just hired? They’re tasked with analyzing data from many different standalone security products that don’t integrate with each other. These different products all require different knowledge levels and skill sets to operate and maintain, and each one takes time. A recent Cisco CISO benchmark study indicates that most organizations find it challenging to orchestrate alerts from different tools, which affects their ability to monitor and correlate information quickly enough to respond to threats before they cause serious damage.
10. New cyberthreats taking advantage of security gaps
Advanced cyberthreats like ransomware and remote access trojans (RATs) take advantage of a lack of visibility and control in a distributed network. Remote and roaming users are particularly susceptible because the traditional centralized security model doesn’t protect them effectively. That’s why 68% of organizations experienced attacks in which a branch location or roaming user was the source of compromise.
Putting it all together
Your organization needs to consider innovative new networking and security options to address today’s challenges successfully. It might feel overwhelming, but we’re here to help you get started on the journey. Read our ebook Secure Access Service Edge (SASE) for Dummies to learn how cloud-delivered networking and security can transform your organization for the better. In just five short chapters, you’ll be well on your way to a better experience for your users and less stress for your IT team.
Lorraine Bellon is a content marketing manager for cloud security at Cisco Systems. Read more Cisco Systems guest blogs here.




