
Over the past few weeks, we have been patiently awaiting a surge in malicious email activity surrounding the novel Coronavirus outbreak that has garnered headlines across the globe. We had previously spotted some run-of-the-mill spam campaigns that were leveraging the outbreak to hawk over-ear facemasks. We subsequently saw some activity from the Emotet malware group that was exploiting the topic by sending mal-spam links. However, those were limited in scale and seemed to be only targeting users in Japan.
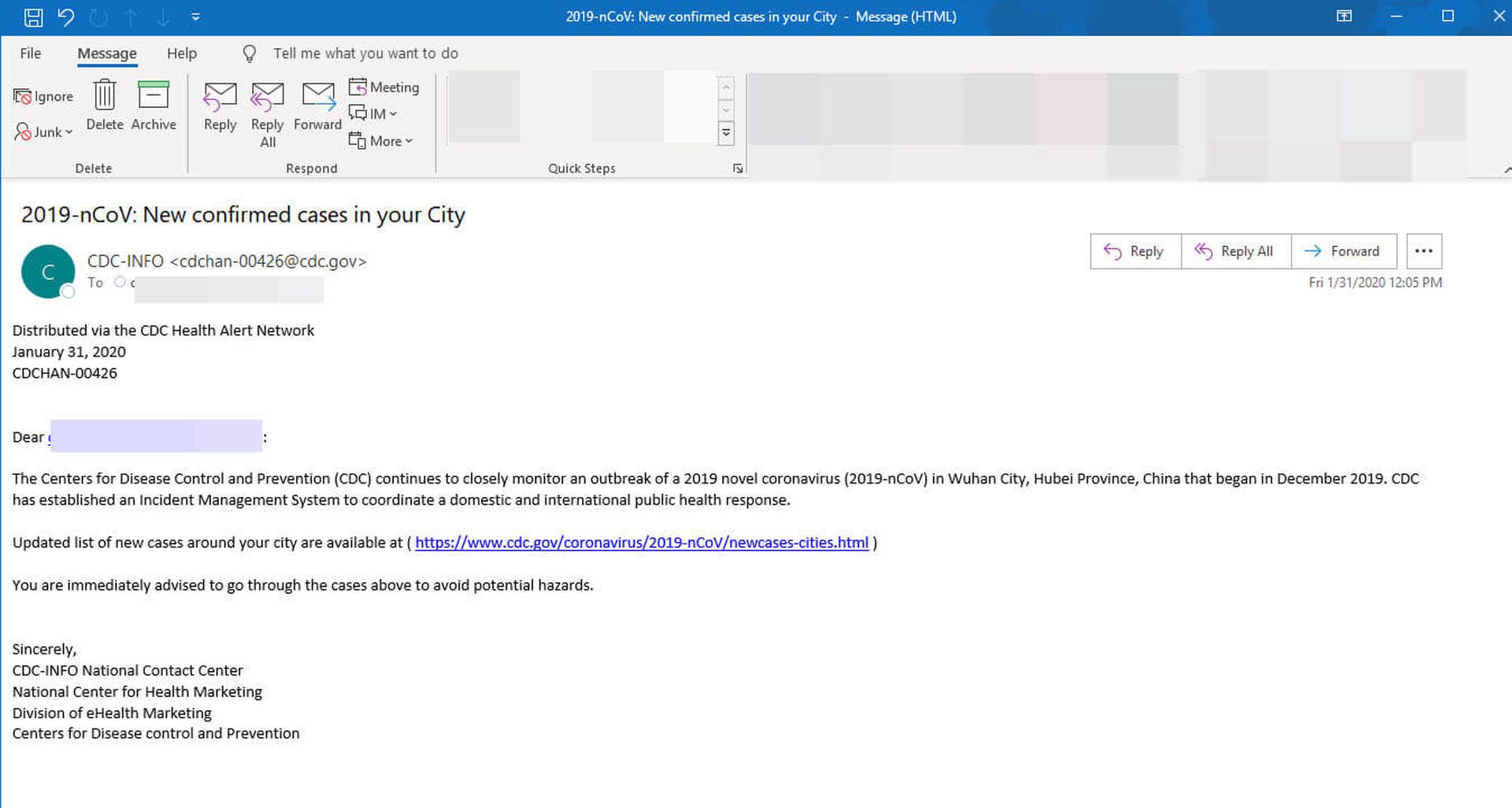
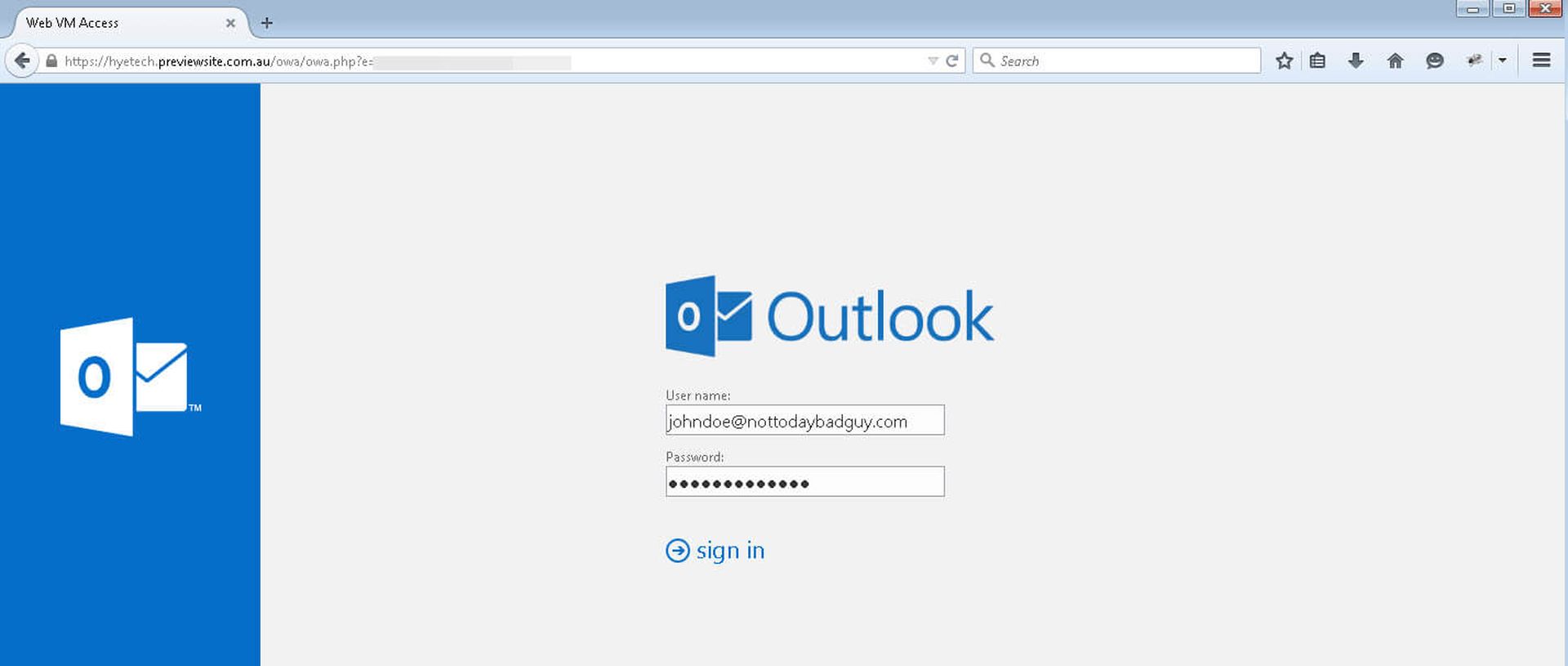
Today, we began monitoring a phishing campaign that poses as an alert from the CDC and appears to have wider distribution. The email, which is made to appear from the Centers for Disease Control and Prevention, claims to provide a list of novel Corona cases “around your city” and advise that the recipient go through the cases to avoid exposure to the virus. However, the links in the message lead to a phony OWA login page designed to harvest email credentials.
Here’s a look at the message and corresponding phishing page:
Phishing for email credentials has certainly become big business in the last several years as attackers leverage the hacked accounts in malware attacks, BECs, supply chain attacks and lots more. We fully expect to see more activity, on the part of cybercriminals, piggybacking on the fear associated with the Coronavirus outbreak. This will likely be amplified if the outbreak was to worsen significantly.
Remember never to click links in unsolicited emails. If you feel some call to action, then always navigate directly to a trusted site (in this case the CDC) for more information. All our Advanced Email Security customers are protected from this threat.
Author Troy Gill is a researcher and senior security analyst at AppRiver, a Zix company. Read more guest blogs from Zix/AppRiver here.




