More than 200 MSP and cybersecurity executives have surfaced at PerchyCon 2020 -- hosted this week in Tampa, Florida, by Perch Security.
In some ways, this can be considered the first pure MSP and MSSP event focused entirely on cybersecurity best practices. Like many attendees, I arrive at the event with scores of questions about the past, present and future of risk mitigation and cybersecurity best practices.
You likely know the back story leading up to this event: Hackers continue to attack MSPs and their software platforms. Successful attacks, in turn, often trigger ransomware attacks that often spread to end-customers.
MSP Security: Three Pressing Questions
Amid that challenging backdrop, I'll boil down most of my conversations here to three questions:
- Progress Report, Please: Is the MSP industry as a whole -- vendors and service providers -- truly making quantifiable progress in the race to safeguard digital assets from hackers, cyberattacks, ransomware and other nasty events?
- Advancements, Please: If we've made progress, please tell me exactly where.
- Soft Spots, Please: What urgent weak points still need addressing?
ChannelE2E is set to meet, speak and listen to dozens of industry sources. To gain access to the event, we've agreed to keep some vendor-specific strategies and financial models confidential. (Translation: Check in directly with your vendors for pricing updates.)
Still, there will be plenty of on-the-record updates below. Keep checking back for more info.
PerchyCon 2020 Live Blog
Among the chatter we've heard so far...
11. Hackers Hitting MSPs: RDP remains a target. But hackers are now targeting MSP documentation systems and password management systems to learn about and defeat MSP's technical controls, according to Datto CISO Ryan Weeks, a guest speaker on a panel.
10. SOCaaS Dial Tone: There are more than 50 SOC as a Service (SOCaaS) companies. What if there was a SOCaaS dial tone that allowed all those providers to more easily integrate with various security tools? CEO Aharon Chernin shares the vision here.
9. Microsoft Office 365 Threat Detection Service: Perch is launching one. Check in directly with the company for featuring and pricing details.
8. Aharon Chernin, Perch Founder and CEO: Unlike broader conferences like RSA, PerchyCon is designed to be a safe place for MSPs focused on security, he says.
More than 255 MSPs are on the Perch platform, which monitors 750,000 events per second across more than 1 million endpoints, Chernin says.
7. Perch Security Activity: The Perch SOC (security operations center) triaged 1.1 million alerts in 2019. Perch then escalated 7,200 alerts, according to the company.
6. How Perch Security Supports MSPs: Our sister site, MSSP Alert, in July 2019 outlined Perch Security's MSP partner strategy here. The effort includes co-managed threat detection & response (MDR), plus security operations center (SOC) services. So what's new? We'll share details soon.
5. Launch Day: CounterAct Cybersecurity Group, led by MSP veteran George Mach, has emerged from stealth mode with a suite of security services and solutions. The offerings are designed to help MSPs protect themselves and their customers against cyberattacks, according to a prepared statement. Initial details are here from MSSP Alert. We'll follow up with Mach at the conference.
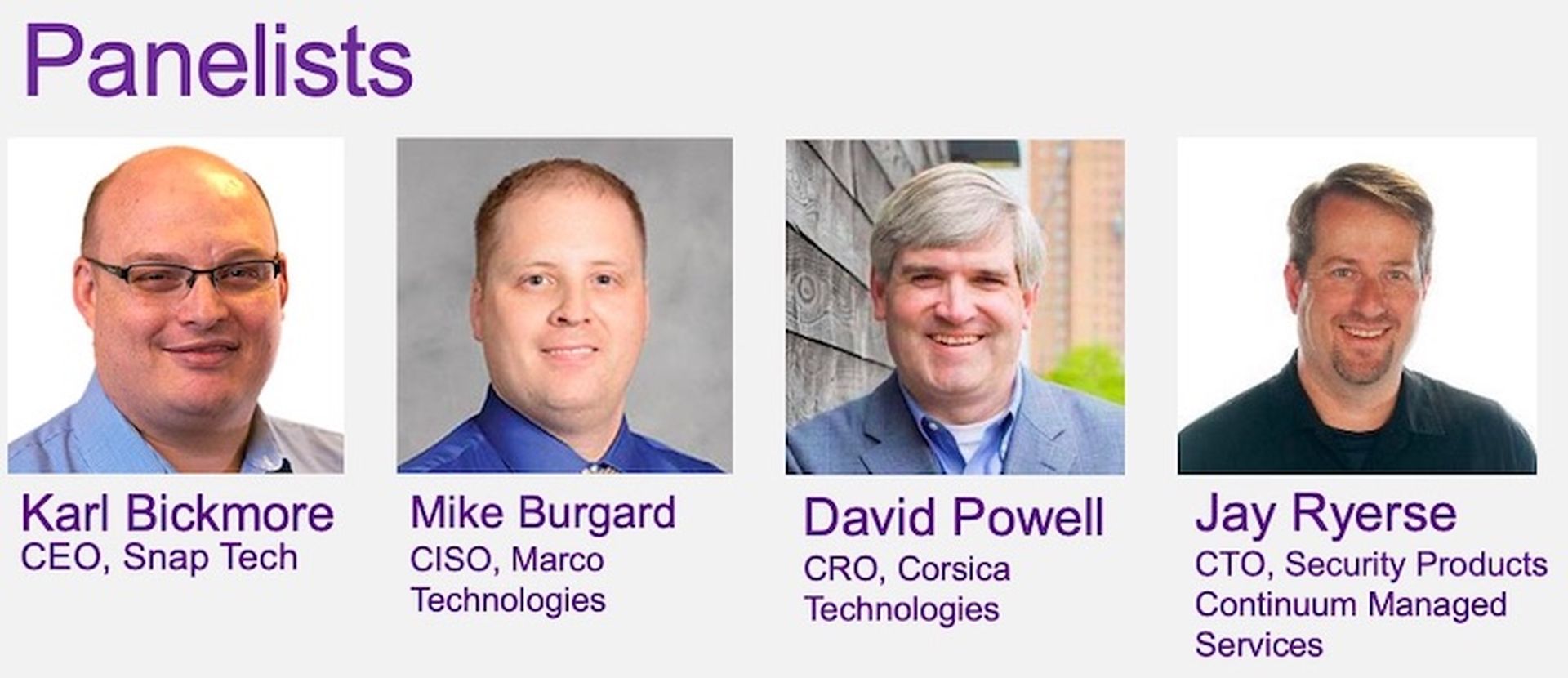
4. MSP Security Pricing Strategies: Is this the classic "price per user" cost model calculation, or are cyber MSPs using new formulas to figure out their cost, profit and pricing models? During a panel conversation, we'll gather thoughts from four rather well-known experts...
3. CISO Insights: Datto's Ryan Week's is expected to be on-hand. Back in October, Weeks explained the MSP path forward for two-factor authentication (2FA). We'll get a progress report on those efforts, and updates on the overall Datto effort to help MSPs safeguard customer assets.
2. The MSP Threat Hunters: Key names to know include Huntress Labs, which always seems to be "in the know" when ransomware hits the MSP community. But who else is on the hunt in the MSP sector? We'll poke around for answers.
1. More Updates: Keep checking back for live updates from the conference. If you're here and potentially want to me, just look for me blogging live somewhere in the main room. Say hi during session breaks, or drop me an email: [email protected].




