Tech scams are on the rise around the world. According to the FBI’s 2016 Internet Crime Report, almost 11,000 tech support scams caused $8 million in losses in that year alone–and that’s just what was reported. Suffice it to say, it benefits all technology solution providers (TSPs) to make sure they’re taking the time to help their customers recognize the red flags before it’s too late.
Use these resources in your customer education efforts...
1. Video Overview
Video link2. What Else to Watch Out For...
Click here to enlarge the file above as a PDF.
Remote Tech Support Scams: A Closer Look
If you work in the technology industry, it’s likely you’ve gotten a call from an upset customer who’s fallen prey to a tech scammer. They saw a pop-up notification offering a free security scan, or received a scary email informing them that their computer was infected and all their files were at risk. Or maybe they got a phone call from a someone claiming to be a support technician from a trusted company advising them to hand over control of their machine right away to prevent further disaster.
Disturbed by the notion that they might lose all their data, they complied with the instructions and allowed the stranger on the other side to remotely access their machine. It’s possible that they’ve received legitimate remote support in the past, so they knew what to expect. After all, even the caller ID looked legit.
Unfortunately, you know all too well how the story ends. The scammer gains access to the device and then requests payment for fixing a non-existent issue, and possibly installs malware or spyware for easy access later. Your customer is left feeling violated and confused. Now, they’re knocking down your door for help.
Customer Education is Key
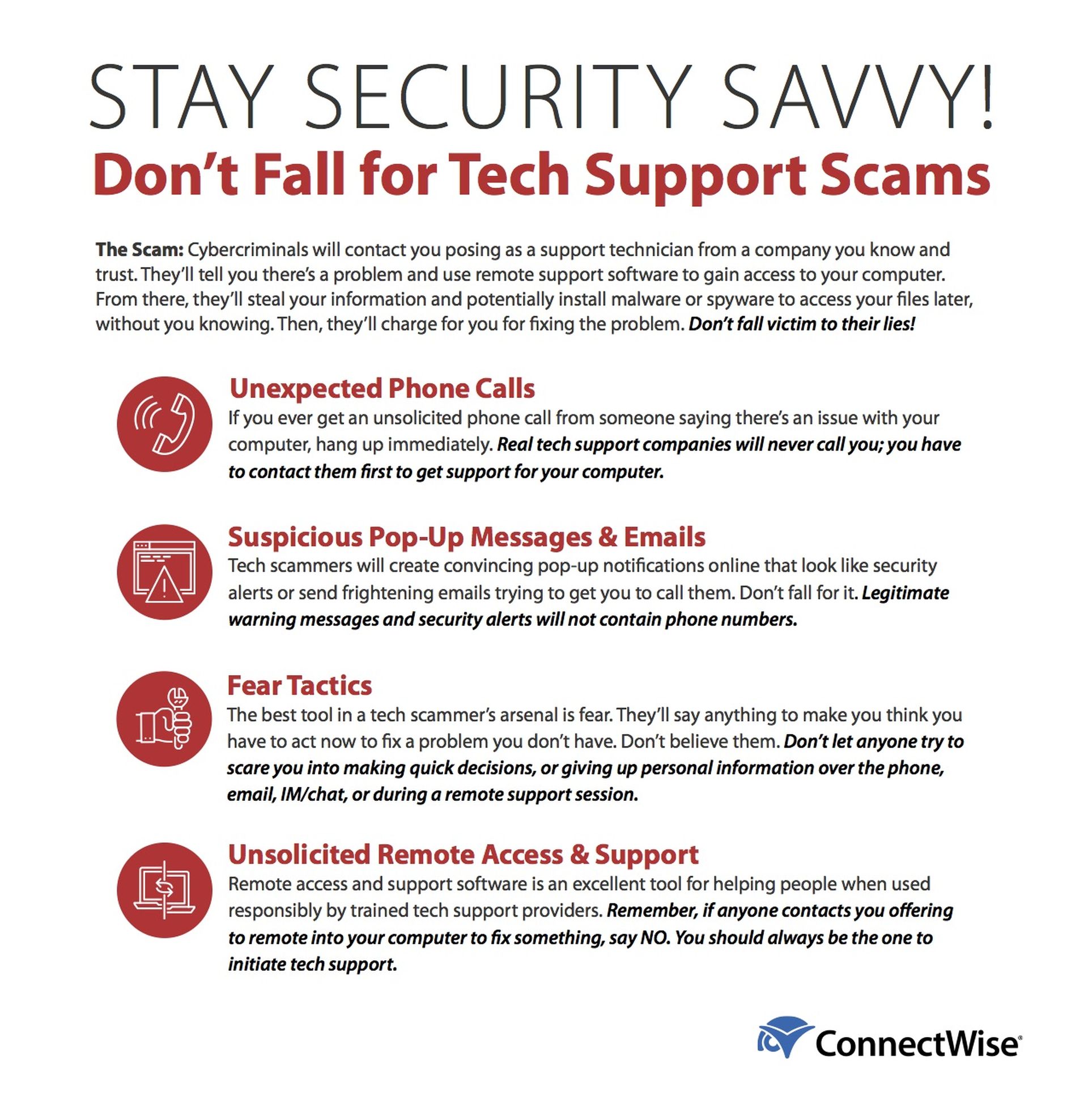
Getting ahead of the situation with customer education will play a key role in keeping your end users safe. Use the document and video above to help reinforce these warning signs:
- Unexpected Phone Calls
- Let them know that if they ever receive an unsolicited phone call from someone saying there’s an issue with their computer, they should hang up immediately. Make sure they understand that your business, and other major tech companies, will never call them proactively to offer remote support services.
- Suspicious Pop-Up Messages & Emails
- Remind your customers that they should never trust notifications or messages that require them to call a phone number or go to an outside link to fix the issue, no matter how convincing they seem. They should always contact you or a trusted tech company first.
- Fear Tactics
- The most powerful tool in a tech scammer’s arsenal is fear. Make sure your customers know that legitimate technology professionals will never use fear or coercion to gain access to their machine, push them to make quick decisions (“or else”), or ask them to share personal information via chat, email, or phone.
- Unsolicited Remote Support
- If there’s one key thing you impart on your customers, it’s that they should never let someone they don’t know take control of their devices unsolicited. No legitimate company will ever proactively offer tech support. They must always be the ones to initiate those services.
The time and effort you spend showing your customers that you care about their cyber safety will uphold your business as a trustworthy source of technology expertise; after all, you’re the “good guys” in the tech realm.
Secure Remote Support Software
There’s another side to the tech scam coin that plays a role in the safety of your end users, and that’s the remote support and access software you work with. It’s important to choose a solution that comes equipped with user friendly safety features on both sides, that can work to instill confidence in your customers like these:
- Give customers full control over connections to their devices with permissions-based access
- Let them watch the technician with options to chat during the session–or end it–when they choose
- Offer the ability to automatically remove the support client from their device at the end of the session
- Limit tech access to certain functions with role-based security permissions
- Enable session audit capabilities, like video recordings, that capture the details of what took place
- Opt for two-factor authentication for all remote logins
- Encourage customers to frequently update their login credentials (and to choose strong passwords)
- Secure, persistent connections for access that don’t require your customers to take any additional action
- Use LDAP or Active Directory user authorization services
Proactive and continuous customer outreach and education will go a long way for showing that you care about your customers’ cyber safety. And if you pair those efforts with remote support and access software that offers transparency and security, you’ll be well on your way to establishing your business as a trusted technology advisor.
In the end, the better your customers understand how you and the software you use keeps them safe, the more value they’ll see in your services.
Blog courtesy of ConnectWise. Read more ConnectWise blogs here.




